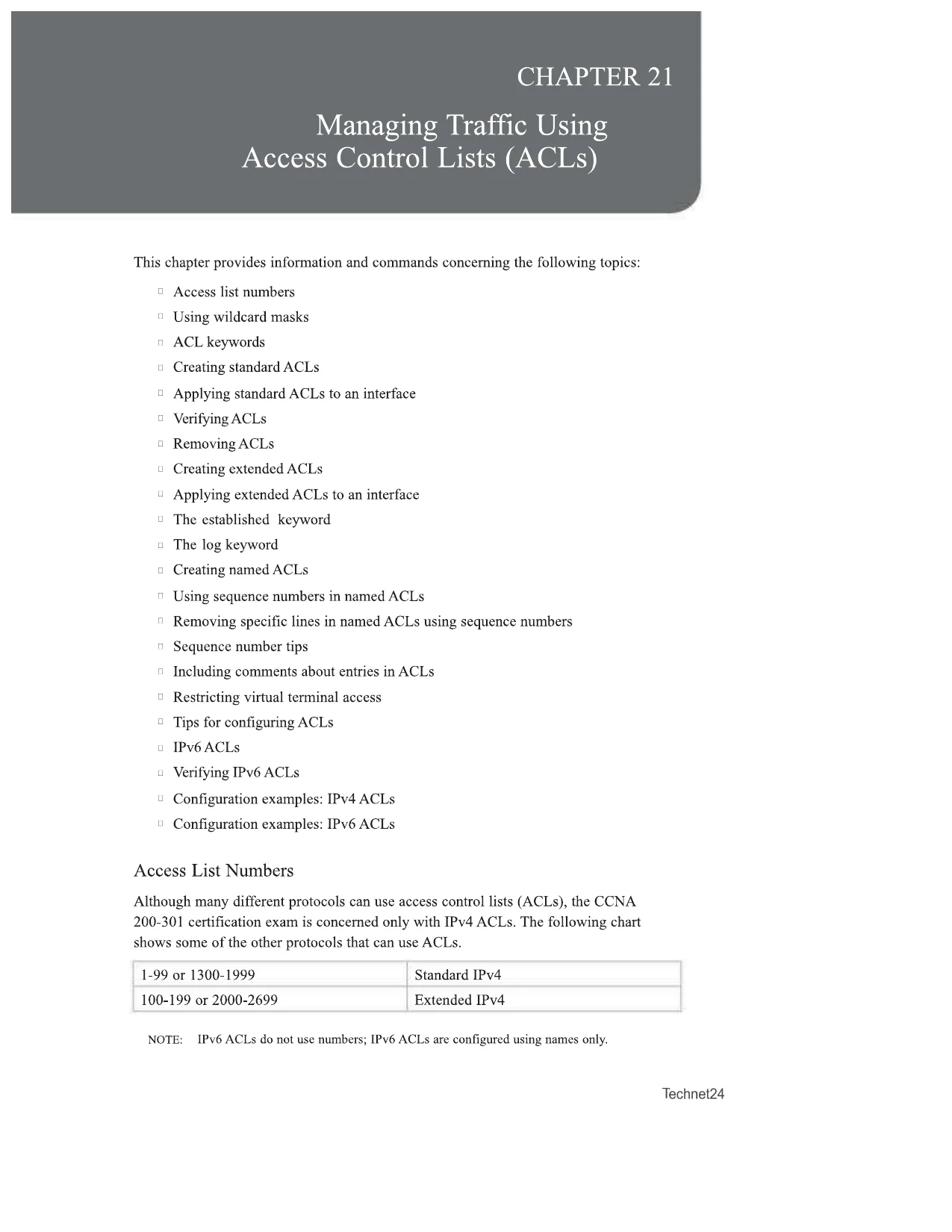
CHAPTER 21Managing Traffic UsingAccess Control Lists (ACLs)This chapter provides information and commands concerning the following topics:DAccess list numbersnUsing wildcard masksn ACL keywords□Creating standard ACLsDApplying standard ACLs to an interfaceDVerifyingACLs□Removing ACLsu Creating extended ACLsuApplying extended ACLs to an interfaceuThe established keyword□The log keyword□Creating named ACLsnUsing sequence numbers in named ACLsnRemoving specific lines in named ACLs using sequence numbersn Sequence number tipsnIncluding comments about entries in ACLsDRestricting virtual terminal access□Tips for configuring ACLsU IPv6 ACLsu Verifying IPv6 ACLsuConfiguration examples: IPv4 ACLsuConfiguration examples: IPv6 ACLsAccess List NumbersAlthough many different protocols can use access control lists (ACLs), the CCNA200-301 certification exam is concerned only with IPv4 ACLs. The following chartshows some of the other protocols that can use ACLs.1-99 or 1300-1999Standard IPv4100-199 or 2000-2699Extended IPv4NOTE:IPv6 ACLs do not use numbers; IPv6 ACLs are configured using names only.Technet24
CHAPTER 21Managing Traffic UsingAccess Control Lists (ACLs)This chapter provides information and commands concerning the following topics:DAccess list numbersnUsing wildcard masksn ACL keywords□Creating standard ACLsDApplying standard ACLs to an interfaceDVerifyingACLs□Removing ACLsu Creating extended ACLsuApplying extended ACLs to an interfaceuThe established keyword□The log keyword□Creating named ACLsnUsing sequence numbers in named ACLsnRemoving specific lines in named ACLs using sequence numbersn Sequence number tipsnIncluding comments about entries in ACLsDRestricting virtual terminal access□Tips for configuring ACLsU IPv6 ACLsu Verifying IPv6 ACLsuConfiguration examples: IPv4 ACLsuConfiguration examples: IPv6 ACLsAccess List NumbersAlthough many different protocols can use access control lists (ACLs), the CCNA200-301 certification exam is concerned only with IPv4 ACLs. The following chartshows some of the other protocols that can use ACLs.1-99 or 1300-1999Standard IPv4100-199 or 2000-2699Extended IPv4NOTE:IPv6 ACLs do not use numbers; IPv6 ACLs are configured using names only.Technet24Preview Mode
This document has 15 pages. Sign in to access the full document!