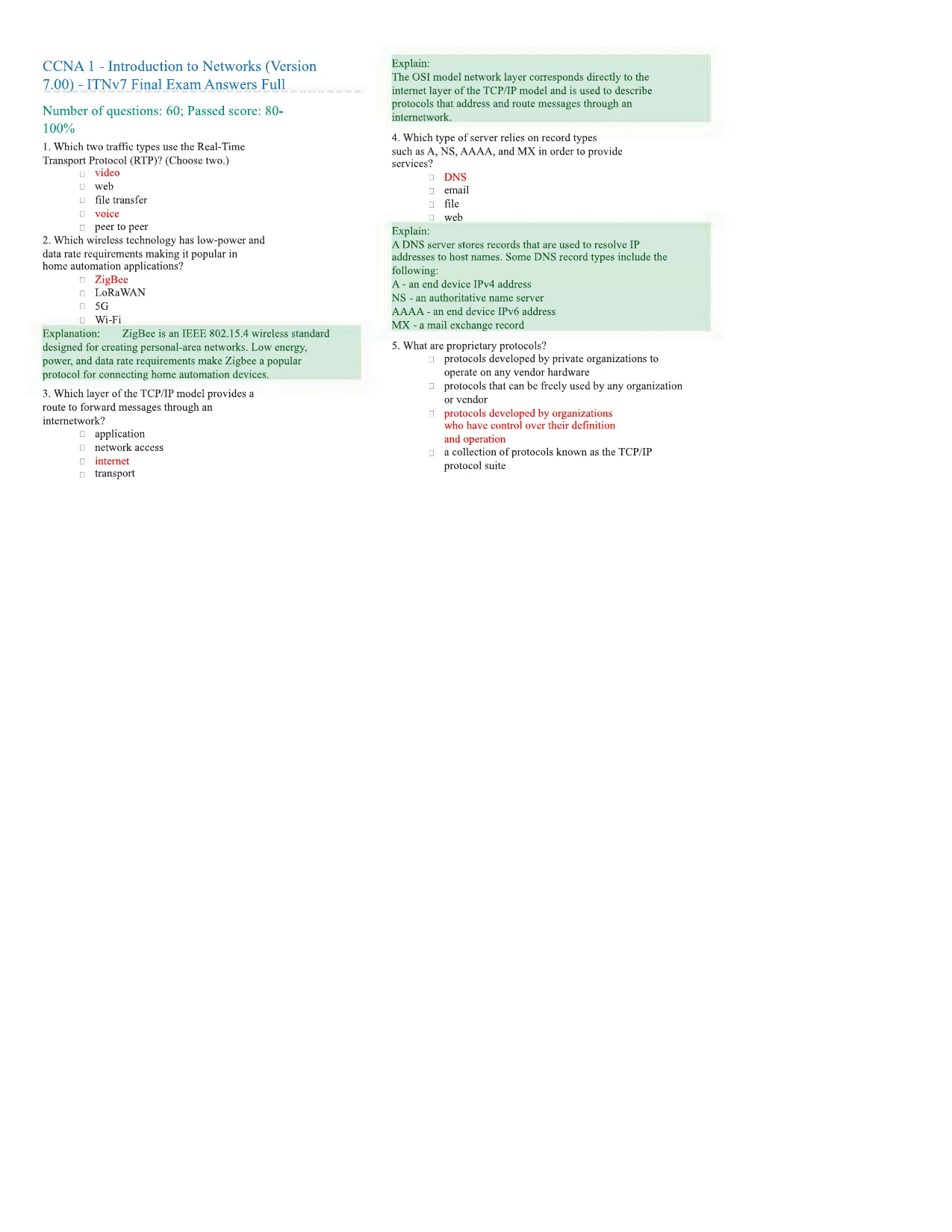
Explain:The OSI model network layer corresponds directly to theinternet layer of the TCP/IP model and is used to describeprotocols that address and route messages through aninternetwork.4. Which type of server relies on record typessuch as A, NS, AAAA, and MX in order to provideservices?□DNS_email□file□webExplain:A DNS server stores records that are used to resolve IPaddresses to host names. Some DNS record types include thefollowing:A - an end device IPv4 addressNS - an authoritative name serverAAAA - an end device IPv6 addressMX - a mail exchange record5. What are proprietary protocols?jprotocols developed by private organizations tooperate on any vendor hardware□protocols that can be freely used by any organizationor vendorprotocols developed by organizationswho have control over their definitionand operationza collection of protocols known as the TCP/IPprotocol suiteCCNA 1 - Introduction to Networks (Version7.00) - ITNv7 Final Exam Answers FullNumber of questions: 60; Passed score: 80-100%1. Which two traffic types use the Real-TimeTransport Protocol (RTP)? (Choose two.)uvideouwebufile transfer□voice□peer to peer2. Which wireless technology has low-power anddata rate requirements making it popular inhome automation applications?nZigBeenLoRaWANn5GWi-FiExplanation:ZigBee is an IEEE 802.15.4 wireless standarddesigned for creating personal-area networks. Low energy,power, and data rate requirements make Zigbee a popularprotocol for connecting home automation devices.3. Which layer of the TCP/IP model provides aroute to forward messages through aninternetwork?□application□network access□internetntransport
Explain:The OSI model network layer corresponds directly to theinternet layer of the TCP/IP model and is used to describeprotocols that address and route messages through aninternetwork.4. Which type of server relies on record typessuch as A, NS, AAAA, and MX in order to provideservices?□DNS_email□file□webExplain:A DNS server stores records that are used to resolve IPaddresses to host names. Some DNS record types include thefollowing:A - an end device IPv4 addressNS - an authoritative name serverAAAA - an end device IPv6 addressMX - a mail exchange record5. What are proprietary protocols?jprotocols developed by private organizations tooperate on any vendor hardware□protocols that can be freely used by any organizationor vendorprotocols developed by organizationswho have control over their definitionand operationza collection of protocols known as the TCP/IPprotocol suiteCCNA 1 - Introduction to Networks (Version7.00) - ITNv7 Final Exam Answers FullNumber of questions: 60; Passed score: 80-100%1. Which two traffic types use the Real-TimeTransport Protocol (RTP)? (Choose two.)uvideouwebufile transfer□voice□peer to peer2. Which wireless technology has low-power anddata rate requirements making it popular inhome automation applications?nZigBeenLoRaWANn5GWi-FiExplanation:ZigBee is an IEEE 802.15.4 wireless standarddesigned for creating personal-area networks. Low energy,power, and data rate requirements make Zigbee a popularprotocol for connecting home automation devices.3. Which layer of the TCP/IP model provides aroute to forward messages through aninternetwork?□application□network access□internetntransportPreview Mode
This document has 44 pages. Sign in to access the full document!