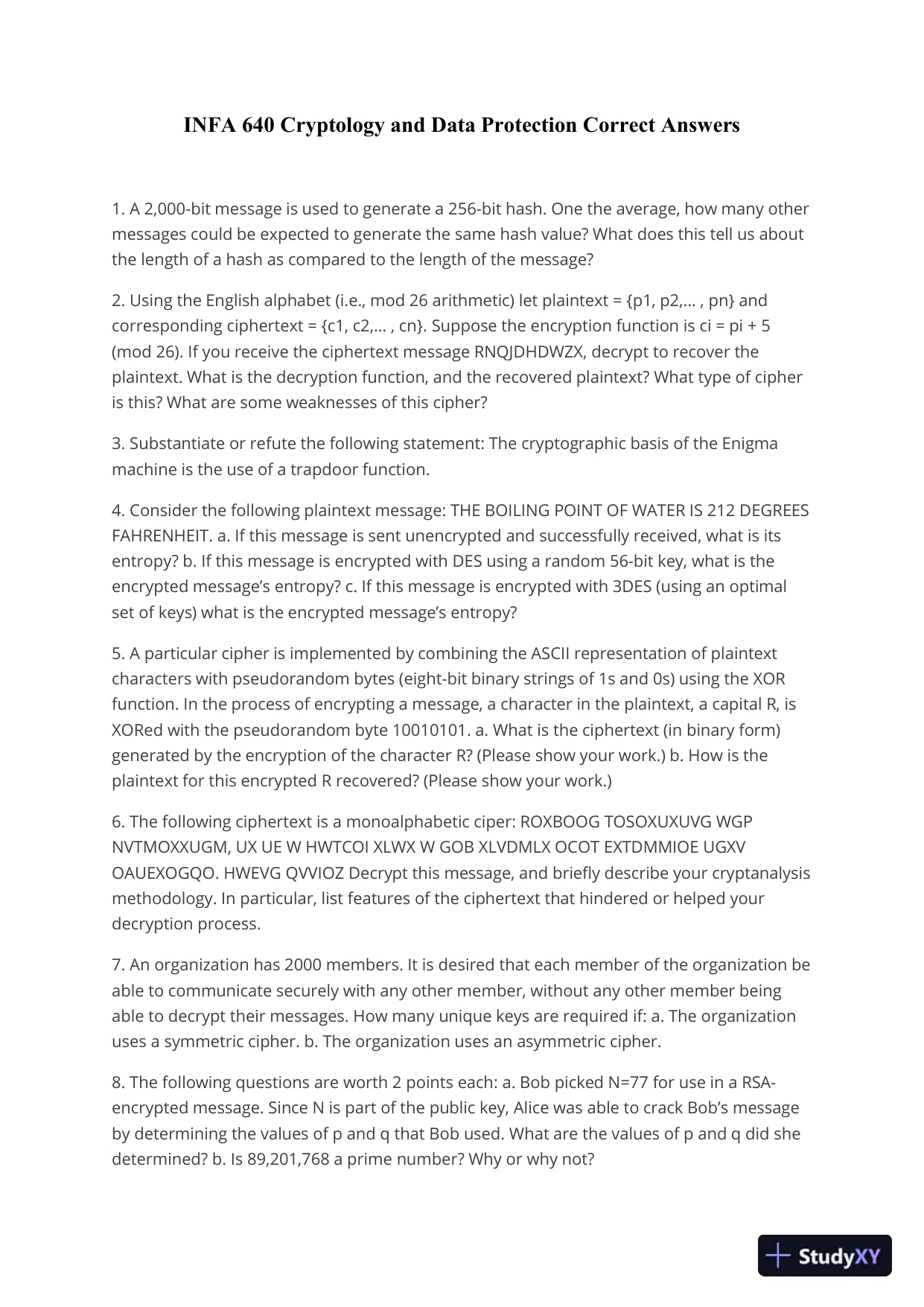
INFA 640 Cryptology and Data ProtectionCorrect Answers1. A 2,000-bit message is used to generate a 256-bit hash. One the average, how many othermessages could be expected to generate the same hash value? What does this tell us aboutthe length of a hash as compared to the length of the message?2. Using the English alphabet (i.e., mod 26 arithmetic) let plaintext = {p1, p2,… , pn} andcorresponding ciphertext = {c1, c2,… , cn}. Suppose the encryption function is ci = pi + 5(mod 26). If you receive the ciphertext message RNQJDHDWZX, decrypt to recover theplaintext. What is the decryption function, and the recovered plaintext? What type of cipheris this? What are some weaknesses of this cipher?3. Substantiate or refute the following statement: The cryptographic basis of the Enigmamachine is the use of a trapdoor function.4. Consider the following plaintext message: THE BOILING POINT OF WATER IS 212 DEGREESFAHRENHEIT. a. If this message is sent unencrypted and successfully received, what is itsentropy? b. If this message is encrypted with DES using a random 56-bit key, what is theencrypted message’s entropy? c. If this message is encrypted with 3DES (using an optimalset of keys) what is the encrypted message’s entropy?5. A particular cipher is implemented by combining the ASCII representation of plaintextcharacters with pseudorandom bytes (eight-bit binary strings of 1s and 0s) using the XORfunction. In the process of encrypting a message, a character in the plaintext, a capital R, isXORed with the pseudorandom byte 10010101. a. What is the ciphertext (in binary form)generated by the encryption of the character R? (Please show your work.) b. How is theplaintext for this encrypted R recovered? (Please show your work.)6. The following ciphertext is a monoalphabetic ciper: ROXBOOG TOSOXUXUVG WGPNVTMOXXUGM, UX UE W HWTCOI XLWX W GOB XLVDMLX OCOT EXTDMMIOE UGXVOAUEXOGQO. HWEVG QVVIOZ Decrypt this message, and briefly describe your cryptanalysismethodology. In particular, list features of the ciphertext that hindered or helped yourdecryption process.7. An organization has 2000 members. It is desired that each member of the organization beable to communicate securely with any other member, without any other member beingable to decrypt their messages. How many unique keys are required if: a. The organizationuses a symmetric cipher. b. The organization uses an asymmetric cipher.8. The following questions are worth 2 points each: a. Bob picked N=77 for use in a RSA-encrypted message. Since N is part of the public key, Alice was able to crack Bob’s messageby determining the values of p and q that Bob used. What are the values of pand q did shedetermined? b. Is 89,201,768 a prime number? Why or why not?
INFA 640 Cryptology and Data ProtectionCorrect Answers1. A 2,000-bit message is used to generate a 256-bit hash. One the average, how many othermessages could be expected to generate the same hash value? What does this tell us aboutthe length of a hash as compared to the length of the message?2. Using the English alphabet (i.e., mod 26 arithmetic) let plaintext = {p1, p2,… , pn} andcorresponding ciphertext = {c1, c2,… , cn}. Suppose the encryption function is ci = pi + 5(mod 26). If you receive the ciphertext message RNQJDHDWZX, decrypt to recover theplaintext. What is the decryption function, and the recovered plaintext? What type of cipheris this? What are some weaknesses of this cipher?3. Substantiate or refute the following statement: The cryptographic basis of the Enigmamachine is the use of a trapdoor function.4. Consider the following plaintext message: THE BOILING POINT OF WATER IS 212 DEGREESFAHRENHEIT. a. If this message is sent unencrypted and successfully received, what is itsentropy? b. If this message is encrypted with DES using a random 56-bit key, what is theencrypted message’s entropy? c. If this message is encrypted with 3DES (using an optimalset of keys) what is the encrypted message’s entropy?5. A particular cipher is implemented by combining the ASCII representation of plaintextcharacters with pseudorandom bytes (eight-bit binary strings of 1s and 0s) using the XORfunction. In the process of encrypting a message, a character in the plaintext, a capital R, isXORed with the pseudorandom byte 10010101. a. What is the ciphertext (in binary form)generated by the encryption of the character R? (Please show your work.) b. How is theplaintext for this encrypted R recovered? (Please show your work.)6. The following ciphertext is a monoalphabetic ciper: ROXBOOG TOSOXUXUVG WGPNVTMOXXUGM, UX UE W HWTCOI XLWX W GOB XLVDMLX OCOT EXTDMMIOE UGXVOAUEXOGQO. HWEVG QVVIOZ Decrypt this message, and briefly describe your cryptanalysismethodology. In particular, list features of the ciphertext that hindered or helped yourdecryption process.7. An organization has 2000 members. It is desired that each member of the organization beable to communicate securely with any other member, without any other member beingable to decrypt their messages. How many unique keys are required if: a. The organizationuses a symmetric cipher. b. The organization uses an asymmetric cipher.8. The following questions are worth 2 points each: a. Bob picked N=77 for use in a RSA-encrypted message. Since N is part of the public key, Alice was able to crack Bob’s messageby determining the values of p and q that Bob used. What are the values of pand q did shedetermined? b. Is 89,201,768 a prime number? Why or why not?Preview Mode
This document has 11 pages. Sign in to access the full document!