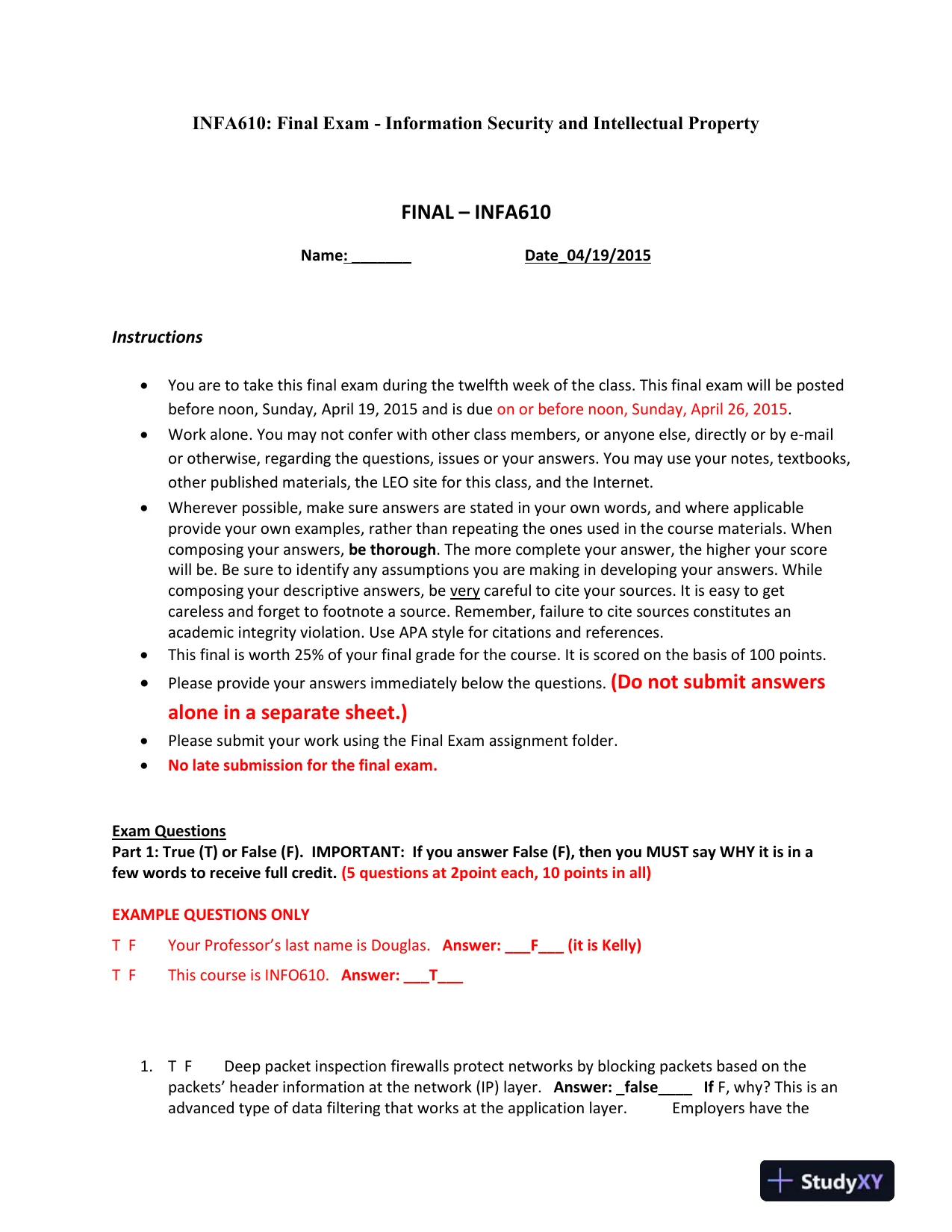
INFA610: Final Exam-Information Security and Intellectual PropertyFINAL–INFA610Name: _______Date_04/19/2015Instructions•You are to take this final exam during the twelfth week of the class. This final exam will be postedbefore noon, Sunday, April 19, 2015 and is dueon or before noon, Sunday, April 26, 2015.•Work alone. You may not confer with other classmembers, or anyone else, directly or by e-mailor otherwise, regarding the questions, issues or your answers. You may use your notes, textbooks,other published materials, the LEO site for this class, and the Internet.•Wherever possible, make sure answers are stated in your own words, and where applicableprovide your own examples, rather than repeating the ones used in the course materials. Whencomposing your answers,be thorough. The more complete your answer, the higher your scorewill be. Be sure to identify any assumptions you are making in developing your answers. Whilecomposing your descriptive answers, beverycareful to cite your sources. It is easy to getcareless and forget to footnote a source. Remember, failure to cite sources constitutes anacademic integrity violation. Use APA style for citations and references.•This final is worth 25% of your final grade for the course. It is scored on the basis of 100 points.•Please provide your answers immediately below the questions.(Do not submit answersalone in a separate sheet.)•Please submit your work using the Final Exam assignment folder.•No late submission for the final exam.Exam QuestionsPart 1: True (T) or False (F). IMPORTANT: If you answer False (F), then you MUST say WHY it is in afew words to receive full credit.(5 questions at 2point each, 10 points in all)EXAMPLE QUESTIONS ONLYT FYour Professor’s last name is Douglas.Answer: ___F___ (it is Kelly)T FThis course is INFO610.Answer: ___T___1.T FDeep packet inspection firewalls protect networks by blocking packets based on thepackets’ header information at the network (IP) layer.Answer: _false____IfF, why? This is anadvanced type of data filtering that works at the application layer.Employers have the
INFA610: Final Exam-Information Security and Intellectual PropertyFINAL–INFA610Name: _______Date_04/19/2015Instructions•You are to take this final exam during the twelfth week of the class. This final exam will be postedbefore noon, Sunday, April 19, 2015 and is dueon or before noon, Sunday, April 26, 2015.•Work alone. You may not confer with other classmembers, or anyone else, directly or by e-mailor otherwise, regarding the questions, issues or your answers. You may use your notes, textbooks,other published materials, the LEO site for this class, and the Internet.•Wherever possible, make sure answers are stated in your own words, and where applicableprovide your own examples, rather than repeating the ones used in the course materials. Whencomposing your answers,be thorough. The more complete your answer, the higher your scorewill be. Be sure to identify any assumptions you are making in developing your answers. Whilecomposing your descriptive answers, beverycareful to cite your sources. It is easy to getcareless and forget to footnote a source. Remember, failure to cite sources constitutes anacademic integrity violation. Use APA style for citations and references.•This final is worth 25% of your final grade for the course. It is scored on the basis of 100 points.•Please provide your answers immediately below the questions.(Do not submit answersalone in a separate sheet.)•Please submit your work using the Final Exam assignment folder.•No late submission for the final exam.Exam QuestionsPart 1: True (T) or False (F). IMPORTANT: If you answer False (F), then you MUST say WHY it is in afew words to receive full credit.(5 questions at 2point each, 10 points in all)EXAMPLE QUESTIONS ONLYT FYour Professor’s last name is Douglas.Answer: ___F___ (it is Kelly)T FThis course is INFO610.Answer: ___T___1.T FDeep packet inspection firewalls protect networks by blocking packets based on thepackets’ header information at the network (IP) layer.Answer: _false____IfF, why? This is anadvanced type of data filtering that works at the application layer.Employers have thePreview Mode
This document has 10 pages. Sign in to access the full document!