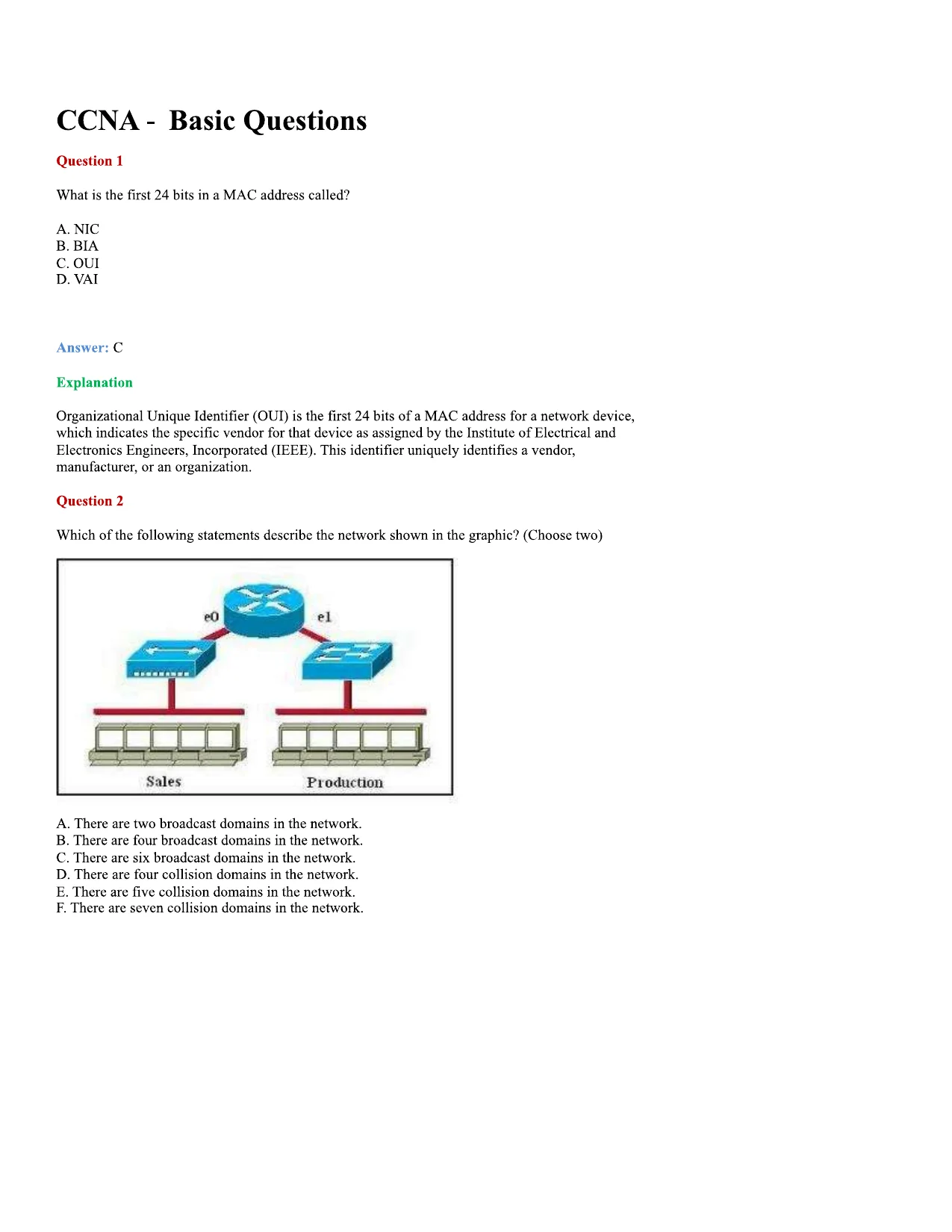
CCNA - Basic QuestionsQuestion 1What is the first 24 bits in a MAC address called?A. NICB. BIAC. GUID. VAIAnswer: CExplanationOrganizational Unique Identifier (GUI) is the first 24 bits of a MAC address for a network device,which indicates the specific vendor for that device as assigned by the Institute of Electrical andElectronics Engineers, Incorporated (IEEE). This identifier uniquely identifies a vendor,manufacturer, or an organization.Question 2Which of the following statements describe the network shown in the graphic? (Choose two)A. There are two broadcast domains in the network.B. There are four broadcast domains in the network.C. There are six broadcast domains in the network.D. There are four collision domains in the network.E. There are five collision domains in the network.F. There are seven collision domains in the network.
CCNA - Basic QuestionsQuestion 1What is the first 24 bits in a MAC address called?A. NICB. BIAC. GUID. VAIAnswer: CExplanationOrganizational Unique Identifier (GUI) is the first 24 bits of a MAC address for a network device,which indicates the specific vendor for that device as assigned by the Institute of Electrical andElectronics Engineers, Incorporated (IEEE). This identifier uniquely identifies a vendor,manufacturer, or an organization.Question 2Which of the following statements describe the network shown in the graphic? (Choose two)A. There are two broadcast domains in the network.B. There are four broadcast domains in the network.C. There are six broadcast domains in the network.D. There are four collision domains in the network.E. There are five collision domains in the network.F. There are seven collision domains in the network.Preview Mode
This document has 259 pages. Sign in to access the full document!