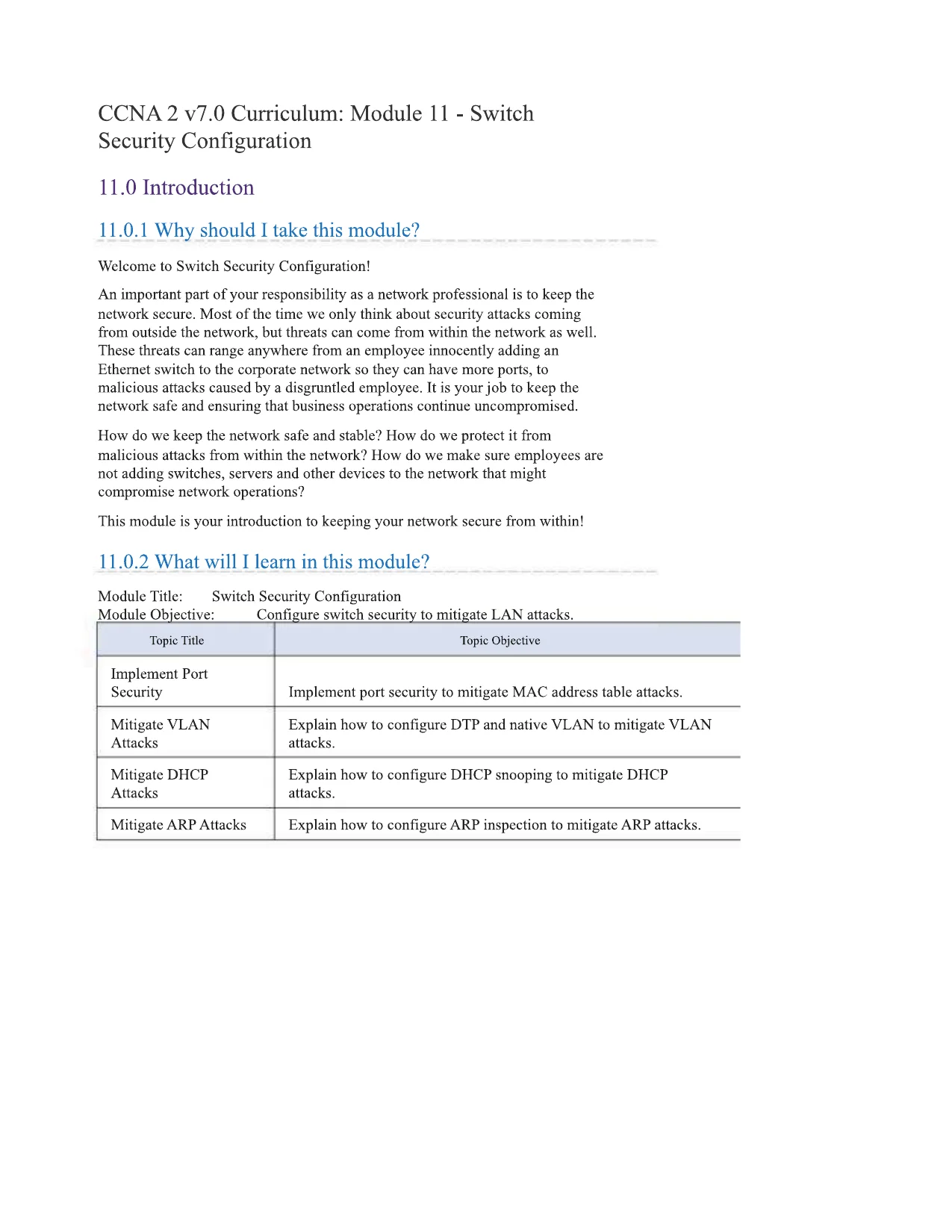
CCNA2 v7.0 Curriculum: Module 11 - SwitchSecurity Configuration11.0 Introduction11.0.1 Why should I take this module?Welcome to Switch Security Configuration!An important part of your responsibility as a network professional is to keep thenetwork secure. Most of the time we only think about security attacks comingfrom outside the network, but threats can come from within the network as well.These threats can range anywhere from an employee innocently adding anEthernet switch to the corporate network so they can have more ports, tomalicious attacks caused by a disgruntled employee. It is your job to keep thenetwork safe and ensuring that business operations continue uncompromised.How do we keep the network safe and stable? How do we protect it frommalicious attacks from within the network? How do we make sure employees arenot adding switches, servers and other devices to the network that mightcompromise network operations?This module is your introduction to keeping your network secure from within!11.0.2 What will I learn in this module?Module Title:Switch Security ConfigurationModule Qbjective:____Configure switch security to mitigate LAN attacks.Topic TitleTopic ObjectiveImplement PortSecurityImplement port security to mitigate MAC address table attacks.Mitigate VLANAttacksExplain how to configure DTP and native VLAN to mitigate VLANattacks.Mitigate DHCPAttacksExplain how to configure DHCP snooping to mitigate DHCPattacks.Mitigate ARP AttacksExplain how to configure ARP inspection to mitigate ARP attacks.
CCNA2 v7.0 Curriculum: Module 11 - SwitchSecurity Configuration11.0 Introduction11.0.1 Why should I take this module?Welcome to Switch Security Configuration!An important part of your responsibility as a network professional is to keep thenetwork secure. Most of the time we only think about security attacks comingfrom outside the network, but threats can come from within the network as well.These threats can range anywhere from an employee innocently adding anEthernet switch to the corporate network so they can have more ports, tomalicious attacks caused by a disgruntled employee. It is your job to keep thenetwork safe and ensuring that business operations continue uncompromised.How do we keep the network safe and stable? How do we protect it frommalicious attacks from within the network? How do we make sure employees arenot adding switches, servers and other devices to the network that mightcompromise network operations?This module is your introduction to keeping your network secure from within!11.0.2 What will I learn in this module?Module Title:Switch Security ConfigurationModule Qbjective:____Configure switch security to mitigate LAN attacks.Topic TitleTopic ObjectiveImplement PortSecurityImplement port security to mitigate MAC address table attacks.Mitigate VLANAttacksExplain how to configure DTP and native VLAN to mitigate VLANattacks.Mitigate DHCPAttacksExplain how to configure DHCP snooping to mitigate DHCPattacks.Mitigate ARP AttacksExplain how to configure ARP inspection to mitigate ARP attacks.Preview Mode
This document has 38 pages. Sign in to access the full document!